We provide hosting, configuration and support for the entire Atlassian product line:
- JIRA Software
- JIRA Service Desk
- JIRA Core
- Confluence
- Bitbucket
- HipChat
- Bamboo
- Clover
- FishEye
- Crucible
- Crowd
Our Services
We provide our Atlassian customers with:
- Complete set-up and installation of the full Atlassian app suite on your own custom domain
- Free migration from Stand Alone applications and Atlassian Cloud on your own hosted instance(s)
- Ability to deploy any plugin and theme to your Atlassian application
- Unmatched expertise in server requirements and server consulting
- Fine tuning of applications for optimum performance
- Configuration and installation of Atlassian application plugins
- 100% network and power uptime guarantees
- Proactive monitoring with Splunk
Our Cloud Infrastructure is HIPAA Compliant
A large and growing number of healthcare providers, payers and IT professionals are using AWS’s utility-based cloud services to process, store, and transmit PHI.
AWS enables covered entities and their business associates subject to the U.S. Health Insurance Portability and Accountability Act (HIPAA) to leverage the secure AWS environment to process, maintain, and store protected health information.
AWS offers a HIPAA-focused Whitepaper for customers interested in learning more about how they can leverage AWS for the processing and storage of health information. The “Creating HIPAA-Compliant Medical Data Applications with AWS” whitepaper outlines how companies can use AWS to process systems that facilitate HIPAA and HITECH compliance.
HIPAA Compliance: A Shared Responsibility Model on AWS
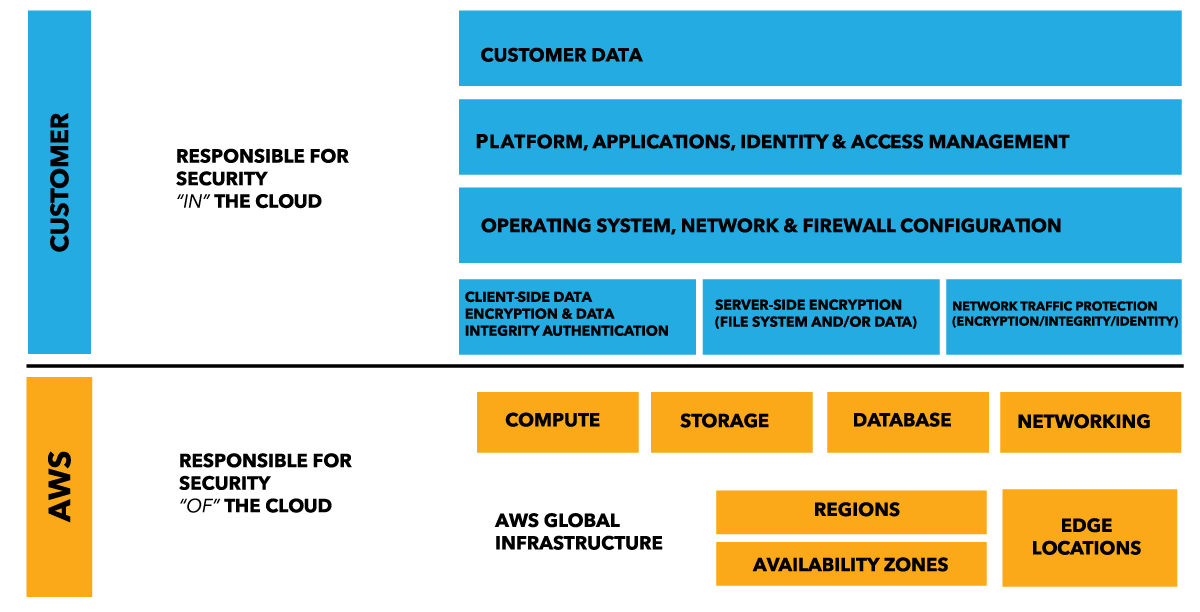
When evaluating the security of a cloud solution, it is important for customers to understand and distinguish between:
- Security measures that the cloud service provider (AWS) implements and operates – “security of the cloud”
- Security measures that the customer implements and operates, related to the security of customer content and applications that make use of AWS services – “security in the cloud”
While AWS manages security of the cloud, security in the cloud is the responsibility of the customer. Customers retain control of what security they choose to implement to protect their own content, platform, applications, systems and networks, no differently than they would for applications in an on-site datacenter.
Easy Cloud in Partnership with Google Cloud is here to help with HIPAA Compliance
For customers who are subject to the requirements of the Health Insurance Portability and Accountability Act (known as HIPAA, as amended, including by the Health Information Technology for Economic and Clinical Health — HITECH — Act), Google Cloud Platform supports HIPAA compliance. This guide is intended for security officers, compliance officers, IT administrators, and other employees who are responsible for HIPAA implementation and compliance on Google Cloud Platform. After reading this guide, you will understand how Google is able to support HIPAA compliance as well as understand how to configure Google Cloud Projects to help meet your responsibilities under HIPAA.
Any capitalized terms used but not otherwise defined in this document have the same meaning as in HIPAA. Furthermore, for the purposes of this document, Protected Health Information (PHI) means the PHI Google receives from a Covered Entity.
It is important to note that there is no certification recognized by the US HHS for HIPAA compliance and that complying with HIPAA is a shared responsibility between the customer and Google. Specifically, HIPAA demands compliance with the Security Rule, the Privacy Rule, and the Breach Notification Rule. Google Cloud Platform supports HIPAA compliance (within the scope of a Business Associate Agreement) but ultimately customers are responsible for evaluating their own HIPAA compliance.
Our Cloud Infrastructure is GDPR Compliant
Microsoft is serious about earning your trust as shown through their contractual commitments to the General Data Protection Regulation.
Easy Cloud in Partnership with Microsoft is here to help with GDPR Compliance
Please have a look at Microsoft’s white paper How Microsoft Azure Can Help Organizations Become Compliant with the EU General Data Protection Regulation to gain an understanding of how your organization can use currently available features in Azure to optimize your preparation for GDPR compliance. We are here to help you with your compliance efforts in the face of the coming EU law.
Easy Cloud in Partnership with Google Cloud is here to help with GDPR Compliance
On 25 May 2018, the most significant piece of European data protection legislation to be introduced in 20 years will come into force. The EU General Data Protection Regulation (GDPR) replaces the 1995 EU Data Protection Directive. The GDPR strengthens the rights that individuals have regarding personal data relating to them and seeks to unify data protection laws across Europe, regardless of where that data is processed.
You can count on the fact that Google is committed to GDPR compliance across Google Cloud services. We are also committed to helping our customers with their GDPR compliance journey by providing robust privacy and security protections built into our services and contracts over the years.



